What is a brute force attack?
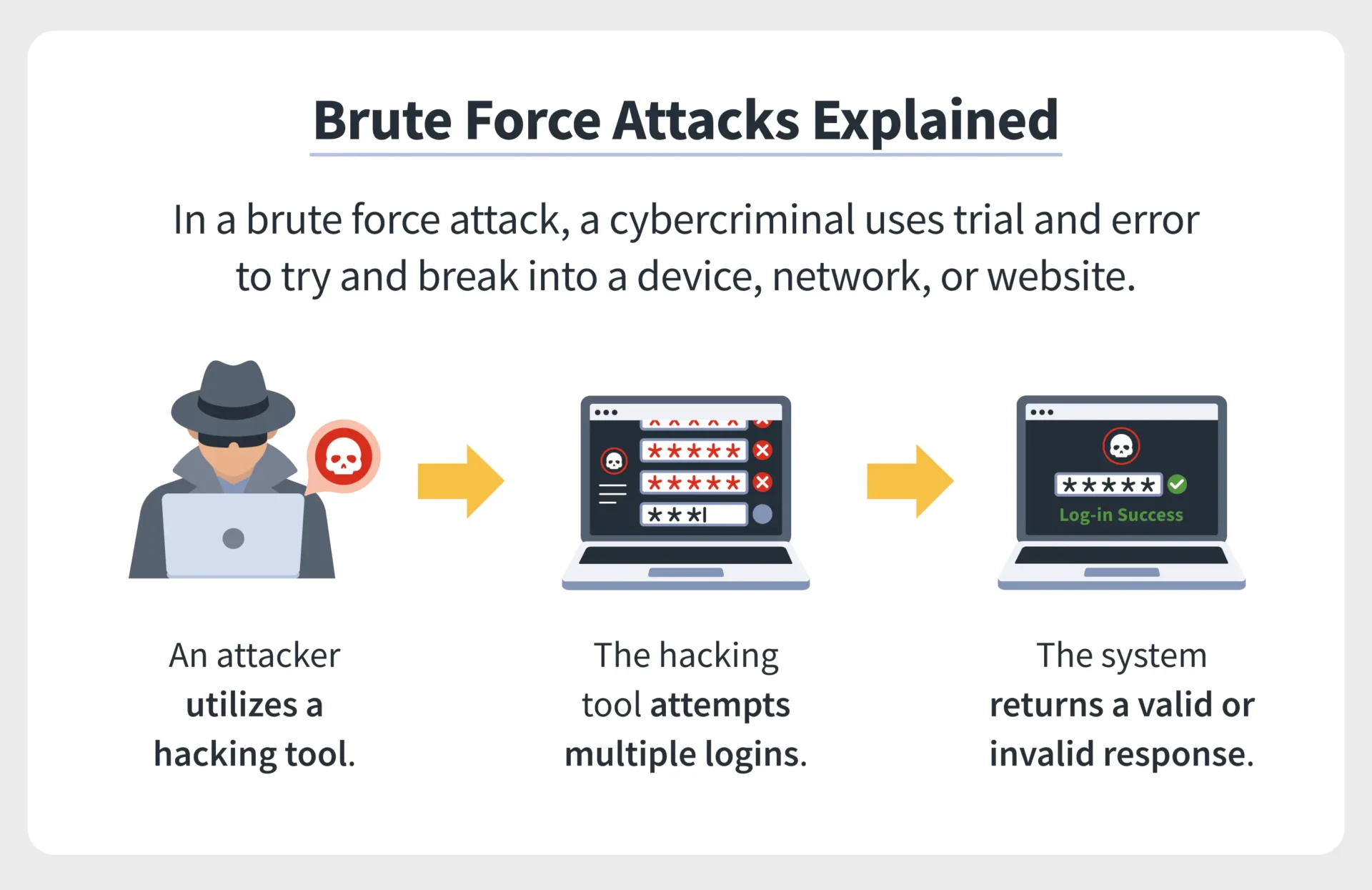
A brute force attack is a trial-and-error method used to decode sensitive data. The most common applications for brute force attacks are cracking passwords and cracking encryption keys (keep reading to learn more about encryption keys). Other common targets for brute force attacks are API keys and SSH logins. Brute force password attacks are often carried out by scripts or bots that target a website’s login page.
What differentiates brute force attacks from other cracking methods is that they don’t employ an intellectual strategy; they try using different combinations of characters until the correct combination is found. This is like a thief trying to break into a combo safe by attempting every possible combination of numbers until the safe opens.
What are the strengths and weaknesses of brute force attacks?
The most significant advantage of brute force attacks is that they are relatively simple. Given enough time and the lack of a mitigation strategy for the target, they always work. Every password-based system and encryption key can be cracked using a brute force attack. The amount of time it takes to brute force into a system is a valuable metric for gauging that system’s level of security.
On the other hand, brute force attacks are prolonged, as they may have to run through every possible combination of characters before achieving their goal. This sluggishness is compounded as the number of characters in the target string increases (a string is just a combination of characters). For example, a four-character password takes significantly longer to brute force than a three-character password, and a five-character password takes substantially longer than a four-character password. Once the character count exceeds a certain point, brute forcing a properly randomized password becomes unrealistic.

If the target string is sufficiently long, it could take a brute-force attacker days, months, or even years to decode a properly randomized password. As a result of the current trend of requiring longer passwords and encryption keys, brute-force attacks are quite a bit more complicated. When good passwords and encryption are utilized, attackers typically try other code-breaking methods, such as social engineering or on-path attacks.
How to protect against brute force attacks
Developers who manage authorization systems can take measures such as locking out IP addresses that have generated too many failed logins and incorporating a delay in their password-checking software. A delay of even a few seconds can significantly weaken the effectiveness of a brute-force attack.
Users of web services can decrease their vulnerability to brute force attacks by choosing longer, more complex passwords. It is also recommended to enable two-factor authentication and use unique passwords for each service. If an attacker can brute force a user’s password for one service, that attacker may try recycling the same login and password on many other popular services. This is known as credential stuffing.
Users should also avoid entering passwords or personal information such as credit card numbers or banking information with any web service that doesn’t protect their data with strong encryption keys.
What is an encryption key?
Encryption keys are random strings of bits generated to scramble and unscramble data. Once the data has been scrambled, it appears as a string of random, chaotic characters until unscrambled with the correct encryption key. Just like passwords, encryption keys can be cracked using brute force attacks, but today there are encryption keys that would take so long to break using modern computers that they are considered as good as unbreakable.
What’s the difference between 128-bit encryption and 256-bit encryption?
A longer encryption key is exponentially more secure than a shorter one. For example, a 128-bit encryption key has 2128 possible combinations a brute force attacker must try. For 256-bit encryption, an attacker must try 2256 combinations, which would require 2128 times more computational power to crack than a 128-bit key! (2128 = 340,282,366,920,938,463,463,374,607,431,768,211,456 possible combinations).
To understand what these numbers mean, a powerful computer that could check trillions of combinations per second would still require over a sexdecillion years to crack a 256-bit encryption key (a sexdecillion is one followed by 96 zeroes).
As high-bit encryption keys are practically immune to current brute-force attacks, it is recommended that all web services that collect user information encrypt their data and communications using 256-bit encryption keys.