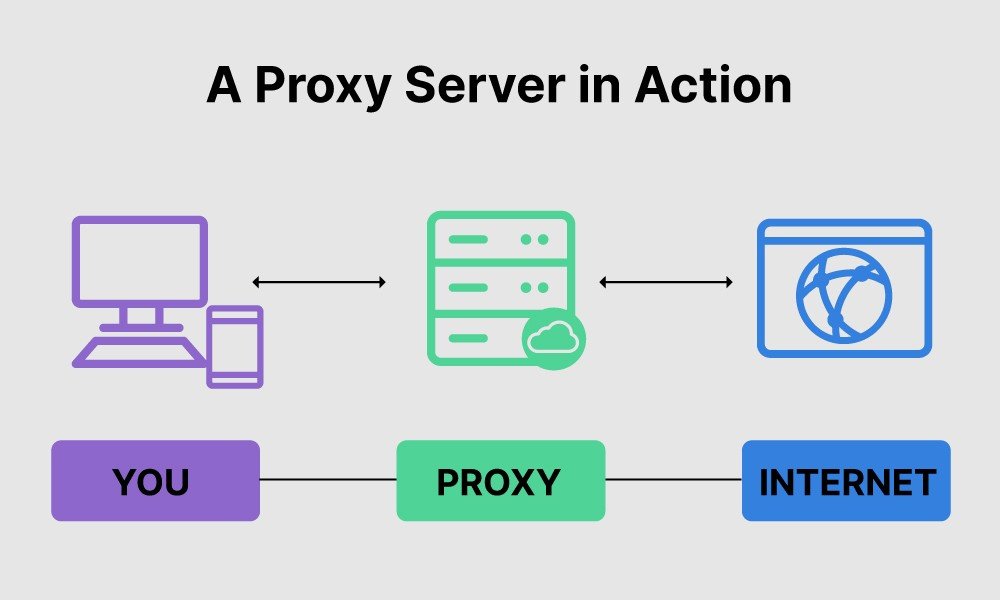
A proxy server is a dedicated computer or software system running on a computer that acts as an intermediary between an endpoint device, such as a computer, and another server from which a user or client requests a service. The proxy server may exist in the same machine as a firewall or on a separate server, which forwards requests through the firewall.
An advantage of a proxy server is that its cache can serve all users. If one or more Internet sites are frequently requested, these are likely to be in the proxy’s cache, improving user response time. A proxy can also log its interactions, which can be helpful for troubleshooting.
How proxy servers work
When a proxy server receives a request for an Internet resource (such as a web page), it looks at its local cache of previous pages. If it finds the page, it returns it to the user without forwarding the request to the Internet. If the page is not in the cache, the proxy server, acting as a client on behalf of the user, uses one of its IP addresses to request the page from the server out on the Internet. When the page is returned, the proxy server relates it to the original request and forwards it to the user.
Proxy servers are used for both legal and illegal purposes. In the enterprise, a proxy server facilitates security, administrative control, or caching services, among other purposes. In a personal computing context, proxy servers enable user privacy and anonymous surfing. Proxy servers can also be used for the opposite purpose: to monitor traffic and undermine user privacy.
To the user, the proxy server is invisible; all Internet requests and returned responses appear to be directly with the addressed Internet server. (The proxy is not invisible; its IP address has to be specified as a configuration option to the browser or other protocol program.)
Users can access web proxies online or constantly configure web browsers to use a proxy server. Browser settings include automatic detection and manual options for HTTP, SSL, FTP, and SOCKS proxies. Proxy servers may serve many users or just one per server. These options are called shared and dedicated proxies, respectively. There are several reasons for proxies and, thus, several types of proxy servers, often in overlapping categories.
Forward and reverse proxy servers
Forward proxies send a client’s requests onward to a web server. Users access forward proxies by directly surfing a web proxy address or configuring their Internet settings. Forward proxies allow the circumvention of firewalls and increase a user’s privacy and security. Still, they may sometimes be used to download illegal materials such as copyrighted materials or child pornography.
Reverse proxies transparently handle all resource requests on destination servers without requiring any action from the requester.
- To enable indirect access when a website disallows direct connections as a security measure.
- To allow for load balancing between servers.
- To stream internal content to Internet users.
- To disable access to a site, for example, when an ISP or government wishes to block a website.
Sites might be blocked for more or less legitimate reasons. Reverse proxies may prevent access to immoral, illegal, or copyrighted content. Sometimes, these reasons are justifiable, and sometimes, they are not. Reverse proxies sometimes prevent access to news sites where users could view leaked information. They can also prevent users from accessing sites where they can disclose information about government or industry actions. Blocking access to such websites may violate free speech rights.
Other types of proxy servers
Transparent proxies are typically found near the exit of a corporate network. These proxies centralize network traffic. On corporate networks, a proxy server is associated with — or is part of — a gateway server that separates the network from external networks (typically the Internet) and a firewall that protects the network from outside intrusion and allows data to be scanned for security purposes before delivery to a client on the network. These proxies help monitor and administer network traffic as the computers in a corporate network are usually safe devices that do not need anonymity for typically mundane tasks.
Anonymous proxies hide the client’s IP address, allowing access to materials blocked by firewalls or circumventing IP address bans. They may be used for enhanced privacy and/or protection from attack.
Highly anonymous proxies hide the fact that clients are using them and present a non-proxy public IP address. So, not only do they hide the IP address of the client using them, but they also allow access to sites that might block proxy servers. Examples of highly anonymous proxies include I2P and TOR.
Socks 4 and 5 proxies provide proxy service for UDP data, DNS lookup operations, and Web traffic. Some proxy servers offer both Socks protocols.
DNS proxies forward domain name service (DNS) requests from LANs to Internet DNS servers while caching for enhanced speed.
Proxy hacking
In proxy hacking, an attacker attempts to steal hits from an authentic web page in a search engine’s index and search results pages. The proxy hacker would have a fraudulent site emulating the original or whatever they felt like showing the clients requesting the page.
Here’s how it works: The attacker creates a copy of the targeted web page on a proxy server and uses keyword stuffing and linking to the copied page from external sites to artificially raise its search engine ranking. The authentic page will rank lower and may be seen as duplicated content, in which case a search engine may remove it from its index.
This form of hacking can also deliver pages with malicious intent. Proxy hacking can direct users to fake banking sites, for example, to steal account info, which can then be sold or used to steal funds from the account. The attacker can also use the hack to direct users to a malware-infected site to compromise their machines for various nefarious purposes.
Some means have been developed to compromise proxy abilities. Specially crafted Flash and Java apps, Javascript, Active X, and some other browser plugins can reveal a proxy user’s identity, so proxies should not be used on untrusted sites or anywhere; anonymity is essential.
Website owners who suspect they have been the victim of a proxy hack can test the theory by searching for a phrase almost uniquely identifying with the site. Their site should be prominent on the search engine results page (SERP). If a second site with the same content shows up, it may be a proxy page.
Proxy server security
Proxy servers, in many forms, enhance security, but like many things in computing, they may be vulnerable. To prevent DoS attacks and network intrusion, administrators should keep software up to date, use load balancing, enforce secure authorization and authentication, and block unsolicited traffic, malicious proxies, and open proxies.